CVE-2026-22208: Security Vulnerabilities in S-100-Based Maritime Navigation Software
Our latest SCIE paper discovers critical RCE vulnerability (CVSS 9.3) in S-100 ECDIS portrayal engine, demonstrating that automated SAST tools miss 83% of expert-identified security flaws.
Analysis of Security Vulnerabilities in S-100-Based Maritime Navigation Software
Our latest research paper has been published in Sensors (SCIE), uncovering critical security vulnerabilities in the S-100 standard used for next-generation Electronic Chart Display and Information Systems (ECDIS).
- Journal: Sensors, Vol. 26, No. 4, p.1246, 2026
- Authors: Hoyeon Cho, Changui Lee, Seojeong Lee
- Affiliations: Korea Maritime & Ocean University; SemanticWave
- DOI: 10.3390/s26041246
- Special Issue: Cyber Physical System: Security and Resilience Challenges and Solutions
CVE-2026-22208
A Common Vulnerabilities and Exposures (CVE) identifier was assigned for the critical vulnerability discovered in this research:
- CVE ID: CVE-2026-22208
- CVSS Score: 9.3 (Critical)
- Type: Remote Code Execution (RCE)
- Vector: Malicious Portrayal Catalogue containing weaponized Lua scripts
Key Findings
The Vulnerability
The S-100 standard uses Lua scripts within Portrayal Catalogues to render electronic navigational charts. However, the standard lacks security specifications for script execution. We discovered that OpenS100, a reference implementation for next-generation ECDIS, runs an unrestricted Lua interpreter — granting full access to os, io, debug, loadfile, and dofile libraries.
This means a malicious Portrayal Catalogue can:
- Execute arbitrary system commands
- Read/write files on the host system
- Establish persistent backdoors
- Exfiltrate sensitive navigation data
SAST Tools vs. Expert Review
We evaluated four automated Static Application Security Testing (SAST) tools against expert manual security review:
| Method | Vulnerabilities Found | Detection Rate |
|---|---|---|
| SAST Tools (combined) | 4 of 23 | 17% |
| Expert Manual Review | 23 of 23 | 100% |
Automated tools failed to detect 83% (19/23) of expert-identified vulnerabilities, including the critical RCE flaw. The primary reasons:
- Limited maritime domain knowledge — tools lack understanding of S-100 standard semantics
- Cross-language blind spots — unable to trace security risks across the C++–Lua interface
- Specification-level flaws — tools focus on code bugs, not design-level security gaps
Root Cause: Specification Gap
The vulnerabilities stem from gaps in the S-100 standard itself, not isolated coding errors. The IHO S-100 Part 9a specifies the use of Lua for portrayal but does not mandate:
- Script sandboxing
- Library restrictions
- Input validation for catalogue files
- Integrity verification of Lua scripts
RCE Demonstration
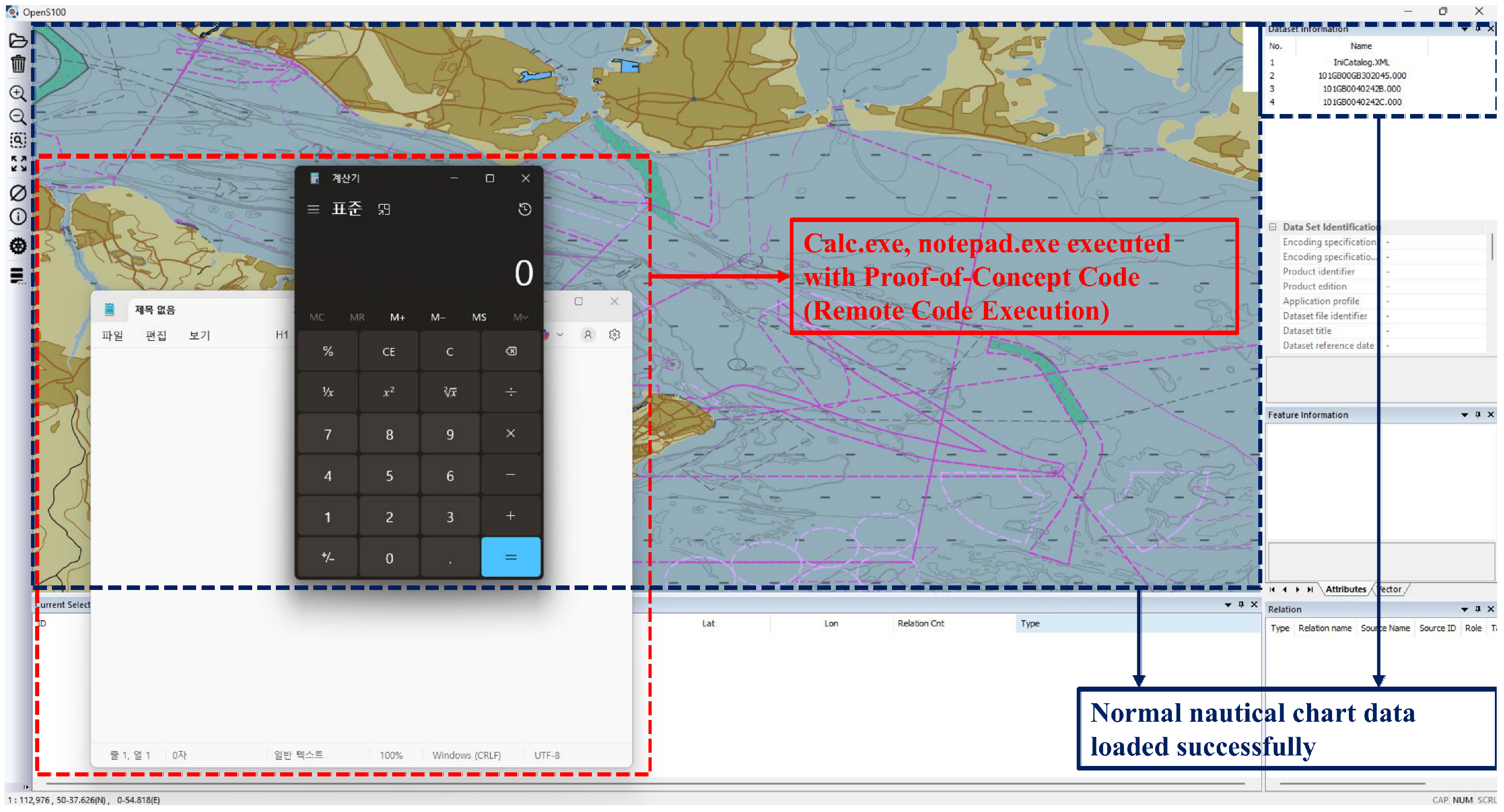 Proof-of-Concept: calc.exe and notepad.exe executed via malicious Portrayal Catalogue while normal nautical chart data loads successfully in OpenS100
Proof-of-Concept: calc.exe and notepad.exe executed via malicious Portrayal Catalogue while normal nautical chart data loads successfully in OpenS100
Exploitation Lifecycle
1
2
3
4
5
6
7
8
9
10
11
Attacker crafts malicious Portrayal Catalogue
↓
Catalogue distributed via supply chain
(update server, USB, network share)
↓
ECDIS loads Portrayal Catalogue
↓
Unrestricted Lua interpreter executes malicious scripts
↓
Remote Code Execution achieved
(data exfiltration, persistent backdoor, system compromise)
Recommendations
The paper proposes that the International Hydrographic Organization (IHO) incorporate the following security controls into the S-100 framework before the 2029 mandatory adoption deadline:
- Script Sandboxing — Restrict Lua execution to safe libraries only (
base,string,table,math) - Library Restrictions — Disable
os,io,debug,loadfile,dofile - Catalogue Integrity Verification — Cryptographic signatures for Portrayal Catalogues
- Restricted File System Access — Limit searchable paths to the Portrayal Catalogue directory only
These recommendations are already implemented in our FerriteS100 project as a reference for secure S-100 portrayal engine design.
Significance
This is the first published CVE targeting the S-100 maritime navigation standard. The findings demonstrate that:
- Functional safety certifications alone are insufficient — security must be addressed at the design level
- Automated tools cannot replace expert security review for domain-specific maritime software
- The S-100 standard requires urgent security amendments before its mandatory adoption in 2029
Citation
1
2
3
4
5
6
7
8
9
10
11
@article{cho2026s100security,
title={Analysis of Security Vulnerabilities in S-100-Based Maritime Navigation Software},
author={Cho, Hoyeon and Lee, Changui and Lee, Seojeong},
journal={Sensors},
volume={26},
number={4},
pages={1246},
year={2026},
publisher={MDPI},
doi={10.3390/s26041246}
}